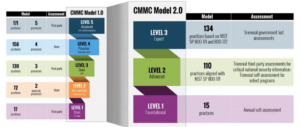
The Cybersecurity Maturity Model Certification (CMMC) has become a crucial consideration for any organization in the Defense Industrial Base (DIB). There are three different CMMC compliance levels, each with a different number of controls. Which level is required for your organization depends on the type of sensitive data handled and the level of compliance has a drastic impact on overall costs.
This article will help you navigate the CMMC certification process and identify the correct CMMC level. We’ll delve into the requirements of each CMMC level, and lay out the steps to achieve compliance.
How to determine which CMMC Level is right for your organization?
The answer to this question is fairly straightforward but anything but simple. These are the two points that organizations need to keep in mind:
- Any covered contract information system that processes, stores or transmits Controlled Unclassified Information (CUI) will need to be at least Level 2.
- If an organization handles (HVA) CUI they will have to achieve Level 3
Here is a quick breakdown of the CMMC v2.0 levels:
What are the CMMC Requirements?
CMMC Level 1 Requirements:
CMMC Level 1, the foundation for all higher levels, focuses on safeguarding Federal Contract Information (FCI). Organizations that sell a product or service to the government must implement the controls found in FAR clause 52.204-21. These controls touch upon various aspects, including:
- Access Control: Restricting access to systems and data based on user permissions.
- Identification and Authentication: Verifying the legitimacy of users attempting to access systems.
- Media Protection: Implementing appropriate measures to protect sensitive information on removable media and during electronic transmission.
- Physical Protection: Securing physical access to critical IT infrastructure and data.
- System and Communications Protection: Establishing safeguards against malware, unauthorized access, and other security threats.
- System and Information Integrity: Ensuring the accuracy and completeness of information while preventing unauthorized modification or deletion.
Organizations at this level will be able to conduct an annual CMMC self-assessment against these 17 controls.
CMMC Level 2 Requirements:
Building upon the foundation of Level 1, CMMC Level 2 delves deeper into cybersecurity practices, focusing on protecting Controlled Unclassified Information (CUI). The National Institute of Standards and Technology (NIST) created the 800-171 standard to protect CUI in covered contractor information systems.
DFARS clause 252.204-7012 requires organizations that handle CUI to implement the 110 controls found in NIST 800-171. The 14 families of controls are:
- Access Control (AC): This family ensures only authorized individuals, accounts, and processes have access to CUI. They do this based on the principle of least privilege, granting only the minimum access needed for their specific roles.
- Awareness and Training (AT): This family emphasizes providing employees with the necessary training and awareness to understand cybersecurity best practices. This helps them recognize potential threats to CUI, and act responsibly in protecting it.
- Audit and Accountability (AU): This family requires recording and monitoring system activity, user actions, and access attempts. This data helps identify suspicious activity, track CUI access, and hold individuals accountable for their actions.
- Configuration Management (CM): This family emphasizes establishing and maintaining secure configurations for hardware, software, and systems. It ensures these components are set up and maintained in a way that minimizes vulnerabilities and promotes secure operation.
- Identification and Authentication (IA): This family focuses on verifying the identity of users attempting to access CUI. It uses methods like passwords, multi-factor authentication, and digital certificates to ensure only authorized individuals can access sensitive information.
- Incident Response (IR): This family outlines a plan for responding to security incidents involving CUI. It defines procedures for detection, containment, eradication, recovery, and reporting of incidents to minimize damage and ensure timely restoration of normal operations.
- Maintenance (MA): This family ensures IT systems are kept up-to-date and secure through regular patching and configuration management activities. This helps address vulnerabilities and maintain system integrity.
- Media Protection (MP): This family focuses on protecting CUI stored on removable media, such as USB drives and CDs. It involves implementing policies and procedures for secure handling, storage, and transport of physical media. This is designed to prevent unauthorized access or loss.
- Personnel Security (PS): This family establishes procedures for ensuring the trustworthiness of personnel with access to CUI. It may involve background checks, security clearances, and awareness training to minimize the risk of insider threats.
- Physical Protection (PE): This family focuses on safeguarding physical locations where CUI is stored or processed. It includes measures like access control systems, security cameras, and environmental controls. This is to protect systems, data, and personnel from physical threats like theft, damage, or unauthorized access.
- Risk Assessment (RA): This family emphasizes regularly assessing the risks posed to personnel, systems, and information. This involves identifying vulnerabilities, analyzing potential threats, and evaluating the effectiveness of existing controls to ensure they adequately mitigate identified risks.
- Security Assessment (CA): This family requires periodically testing and reviewing the effectiveness of implemented security controls, both logical (software-based) and physical. This helps identify weaknesses, refine control measures, and ensure they meet their intended objectives.
- System and Communications Protection (SC): This family focuses on implementing additional measures to protect CUI data from unauthorized disclosure, interception, modification, or destruction. Encryption is a key element of this control family, but other controls may also be included.
- System and Information Integrity (SI): This family focuses on protecting the accuracy, completeness, and trustworthiness of CUI. It involves implementing controls to prevent unauthorized modification, deletion, or manipulation of information. Thereby ensuring data integrity and preventing reliance on inaccurate or compromised information.
Organizations at this level will no longer be able to conduct an annual self assessment. Instead they will have to undergo a CMMC third-party assessment every three years. These third party assessments are conducted by a CMMC Third Party Assessor Organization (C3PAO’s). A CMMC C3PAO is authorized to conduct these assessments by the CMMC Accreditation Body (CMMC AB).
CMMC Level 3 Requirements:
CMMC Level 3 is designed for organizations handling the highest-priority CUI for the Department of Defense (DoD). It requires implementing additional controls from NIST 800-172. These are on top of the controls from Levels 1 and 2, diving deeper into areas like:
- Security Engineering Practices: Implementing advanced security measures like system hardening, secure coding practices, and penetration testing.
- System and Communications Protection: Employing advanced intrusion detection and prevention systems, secure network segmentation, and encryption technologies.
- Supply Chain Risk Management: Assessing and mitigating cybersecurity risks associated with third-party vendors and partners.
- Physical Security and Environmental Controls: Implementing heightened physical security measures and environmental controls to protect critical infrastructure and data.
- Security Assessment and Continuous Monitoring: Conducting regular independent assessments and implementing continuous monitoring practices to identify and address vulnerabilities proactively.
Steps to Become Compliant:
Begin With a CMMC Self Assessment
Organizations are currently required to conduct an annual CMMC gap assessment. They are then required to submit their SPRS score (Supplier Performance Risk System) to the DoD. This is a great place to start as this will show you your current gaps so you can develop a CMMC compliance plan.
Get expert help to go over your CMMC assessment results
A DoD audit found that the typical company is only approximately 60% compliant with the controls. A certified CMMC assessor will help you develop a CMMC roadmap to address any gaps and gain certification.
Implement Solutions
After getting expert advice, it’s time to implement their recommended solutions. These solutions can range from technical solutions like a SIEM to documentation like policies. By leveraging the expertise of CMMC compliance consultants, organizations can increase their chances of successfully achieving certification.
Conduct an Internal Audit
This is the final step before the actual audit. Our audit professionals will conduct a final walkthrough before the C3PAO to make sure that everything is ready. This includes reviewing your System Security Plans and developing a Plan of Action and Milestones. This will ensure your organization meets the required levels of compliance.
Don’t go through the CMMC compliance process alone. Reach out to the FirstCall Compliance team today to get started.