Understanding Cybersecurity Maturity Model Certification (CMMC): Your Guide to Assessment Levels and Process
The Cybersecurity Maturity Model Certification (CMMC) is a Department of Defense (DoD) program designed to ensure that defense contractors adequately protect sensitive information, specifically Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). The Department of Defense supply chain is vast and complex, making it vulnerable to cyberattacks. CMMC determines a standardized framework to ensure that all contractors, regardless of size, meet minimum cybersecurity requirements.
CMMC will start to be a requirement in contracts later this year, but already prime contractors are starting to require their suppliers to get certified. This means that contractors have two different timelines to be aware of:
-
When will the government require CMMC
-
When will your prime contractor require CMMC
Organizations who fail to meet either deadline risk losing existing DoD contracts and becoming ineligible for future ones.
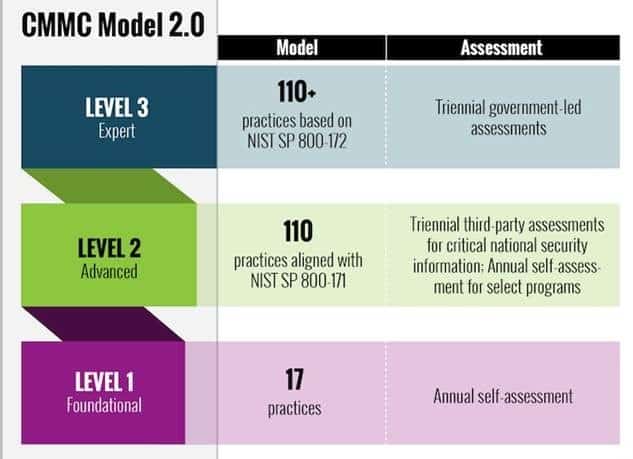
CMMC provides a clear and consistent set of cybersecurity standards that contractors must adhere to, helping to improve overall cybersecurity posture across the defense industrial base. CMMC 2.0 has streamlined the process and contains 3 levels. These levels are based on the type of information a contractor handles. This allows for a more tailored approach to cyber security.
In essence, CMMC is vital for Department of Defense contractors to maintain their eligibility for contracts, protect sensitive data, and contribute to the overall security of the defense supply chain.
Navigating the various Cybersecurity Maturity Model Certification (CMMC) assessment levels
1. Understanding and Identifying CUI and FCI Data:
Accurately identifying and categorizing CUI is a fundamental but complex task. CUI should be (but oftentimes isn’t) appropriately marked by your prime or contracting officer. However, oftentimes these entities do not properly understand what CUI is, and will overmark documents as CUI to protect themselves.
The National Archives and Records Administration (NARA) is responsible for the overall CUI program for the federal government. NARA has a CUI Registry located here that has every categorization of CUI data.
Recently, the DoD released a memo titled, “Implementing the Cybersecurity Maturity Model Certification (CMMC) Program: Guidance for Determining Appropriate CMMC Compliance Assessment Levels and Process for Waiving CMMC Assessment Requirements” that memo can be found here.
In this memo, the DoD states that:
-
???????????????? ???????????????????? ???? (????????????????-????????????????????????????????????????) is the minimum assessment requirement for CUI. It is sufficient only for CUI outside of the National Archive’s CUI Registry Defense Organizational Index Grouping.
???????????????? ???????????????????? ???? (????????????????????????????????????????????????????) is the minimum requirement when the planned contract will require the contractor (or subcontractors) to process, store, or transmit CUI categorized under the National Archive’s CUI Registry Defense Organizational Index Grouping.
This means that organizations who handle any of the following types of information will need a CMMC Level 2 certificate provided by a C3PAO:
Identifying this information is key for organizations to determine whether or not they need to undergo a third party audit. Additionally, contractors must thoroughly map their data flows to understand where CUI resides within their systems, which can be a time-consuming and intricate process.
2. Implementation and Documentation:
Implementing the necessary security controls, developing policies and procedures, and gathering evidence for assessments requires substantial time and resources. Many organizations struggle to meet these stringent requirements. The implementation of technical controls such as multifactor authentication, and encryption can also be difficult for smaller companies.
3. Assessment Preparation and Performance:
Third-party assessments can incur significant costs. Ensuring readiness for assessments involves thorough internal assessments, remediation of identified gaps, and meticulous preparation of documentation. Cybersecurity standards are continually evolving, which means that CMMC requirements can also change. This can make it difficult for companies to keep up.
4. Organizational and Management Challenges:
Upper management may prioritize cost efficiency over cybersecurity investments, creating tension between compliance and business operations. Cultivating a strong cybersecurity culture and ensuring that all employees are aware of their responsibilities is crucial but challenging. CMMC compliance is an ongoing process that requires continuous monitoring and improvement.
Decoding CMMC Assessment Levels: Aligning with Your Contract Requirements
CMMC 2.0 Levels:
Level 1: Foundational: Protection of Federal Contract Information (FCI). Requires the implementation of 17 basic safeguarding requirements outlined in FAR clause 52.204-21. These are fundamental cybersecurity practices. Annual self-assessments are allowed with the results entered into the Supplier Performance Risk System (SPRS).
Level 2: Advanced: Protecting Controlled Unclassified Information (CUI). Requires adherence to the 110 security controls specified in NIST SP 800-171 revision 2. This represents a significant increase in the number of controls from 17 to 110. Assessments can be either self-assessments or third-party assessments conducted by Certified Third-Party Assessment Organizations (C3PAOs), depending on the criticality of the CUI. Assessments occur every three years with an annual affirmation required.
Level 3: Expert: Protection of highly sensitive CUI, particularly for high-priority Department of Defense (DoD) programs. Builds upon Level 2 by incorporating a subset of CMMC security requirements from NIST SP 800-172, which addresses advanced persistent threats (APTs). This level requires implementation of CMMC level 2, and passing an assessment by a C3PAO. Assessments are then conducted by government officials from the Defense Contract Management Agency’s Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) for the delta controls at Level 3. These assessments also occur every three years with an annual affirmation.
The sensitivity and context of the CUI, and the potential impact of its compromise, determine the necessary CMMC level
Understanding the Relationship:
CUI is the information that requires enhanced protection. The CMMC levels are the frameworks for how well that protection must be executed. Any type of CUI could potentially fall under Level 2 or Level 3, depending on its sensitivity and the program it’s associated with.
Level 1 primarily focuses on Federal Contract Information (FCI). While not CUI, FCI can sometimes contain elements that, when combined, could lead to CUI.
Level 2 is the baseline for protecting CUI. This level requires compliance with NIST SP 800-171, which has 110 controls for protecting CUI. Examples of CUI that would require level 2 protection: Personally Identifiable Information (PII), Controlled Technical Information (CTI), Export Control Information, Procurement Information and Legal Information.
Level 3 is for protecting the most sensitive CUI, particularly in high-priority Department of Defense (DoD) programs. It builds upon Level 2 by adding requirements from NIST SP 800-172, which addresses advanced persistent threats (APTs). Level 3 is generally applied to CUI where a compromise would have a severe or catastrophic impact on national security. Examples of CUI that may require Level 3 protection: CUI related to critical infrastructure, CUI related to weapons systems, CUI related to intelligence requiring activities and CUI that if compromised would give a significant advantage to an adversary.
Identifying the required CMMC level for a specific Department of Defense (DoD) contract
1. Review the Request for Proposal (RFP) and Contract Language:
The RFP or contract will eventually explicitly state the required CMMC level. Pay close attention to any clauses related to cybersecurity requirements, CUI, or NIST SP 800-171/800-172. Look for specific language referencing “CMMC Level [number]” or “NIST SP 800-171 compliance.” Carefully analyze the contract’s scope of work to understand the types of information you will be handling. Identify if you will be processing, storing, or transmitting FCI or CUI. Determine how information will flow through your systems and those of your subcontractors. This helps identify where CUI may reside and the necessary safety controls.
2. Analyze the Type of Information Handled:
If the contract only involves FCI, Level 1 is likely sufficient. Remember that even basic federal contract information can have elements that, if aggregated, could lead to CUI. If the contract involves CUI, Level 2 or Level 3 will be required. Use the CUI Registry to determine the specific categories of CUI involved. Assess the sensitivity and potential impact of the CUI to determine if Level 3 is necessary.
3. Consult with the Contracting Officer or Prime Contractor:
If you are unsure about the required CMMC level, seek clarification from the contracting officer or prime contractor. They can provide guidance on the specific cybersecurity requirements for the contract. Request written confirmation of the required CMMC level to ensure clear understanding and avoid future disputes.
4. Consider the Impact of Subcontractors:
If you plan to use subcontractors, ensure that they also meet the required CMMC level. Cybersecurity requirements must flow down to all subcontractors handling FCI or CUI. Assess the cybersecurity maturity of your subcontractors to mitigate supply chain risks.
Conducting a Gap Analysis: Preparing for Your CMMC Assessment
Benefits of Conducting a Gap Analysis:
1. Identifying and Remedying Vulnerabilities:
A gap analysis allows you to pinpoint weaknesses in your cybersecurity posture before a C3PAO does. This proactive approach enables you to address vulnerabilities and strengthen your defenses. Failing an official C3PAO assessment can lead to significant financial losses, including lost contracts and paying for a second assessment. A gap analysis helps you avoid these pitfalls.
2. Optimizing Resource Allocation:
A gap analysis helps you prioritize remediation efforts by identifying the most critical vulnerabilities. Addressing gaps early can be more cost-effective than dealing with them during or after an official assessment.
3. Building Confidence and Demonstrating Due Diligence:
A thorough gap analysis provides you with the confidence that you are prepared for the official assessment. Conducting a gap analysis demonstrates your commitment to cybersecurity and your willingness to take the necessary steps to protect sensitive information.
Steps to Conduct a Gap Analysis
1. Planning and Preparation:
Determine the scope of the assessment, including the systems, information, and personnel involved. First define the CMMC level being targeted and then assemble a team with expertise in cybersecurity, IT, and compliance. Collect applicable documentation, including existing policies, plan of actions, network diagrams, and system configurations. Obtain a copy of the applicable NIST SP 800-171 or 800-172 controls.
2. Policy and Procedure Review:
Review all existing cybersecurity policies and procedures to ensure they align with CMMC requirements. Assess the completeness and accuracy of documentation. Look for gaps in required policies (e.g., incident response, access control, configuration management). Determine if policies are actually being followed. Check for consistent application across the organization.
3. System and Network Assessment:
Conduct vulnerability scans of systems and networks to identify potential weaknesses. Use automated tools to identify known vulnerabilities. Review system configurations to ensure they meet safety best practices. Check for proper access controls, encryption, and logging. Analyze network traffic and logs to identify suspicious activity. Review network architecture for safety weaknesses. Review physical access controls to server rooms, workstations, and other sensitive subjects.
4. Data Security Assessment:
Map the flow of CUI through your systems to identify where it resides and how it is transmitted. Review access controls to ensure that only authorized personnel have access to CUI. Check for proper user authentication and authorization. Assess the use of encryption for information at rest and in transit. Verify that backup and recovery actions are in place and effective.
5. Employee Interviews and Training Assessment:
Conduct interviews with employees to assess their understanding of cybersecurity policies and actions. Gather feedback on the effectiveness of training programs. Review training records to ensure that employees have received appropriate cybersecurity training. Evaluate the effectiveness of the training. Gauge the overall safety awareness of the workforce.
6. Gap Identification and Reporting:
Compare the results of the assessment to the CMMC requirements to identify gaps. Document each gap and its potential impact. Prepare a comprehensive report that outlines the findings of the gap analysis. Include a list of identified gaps, their severity, and recommended remediation actions.
7. Remediation Planning:
Develop a remediation plan that outlines the steps necessary to address each identified gap. Prioritize remediation efforts based on the severity of the gaps. Assign responsibilities for implementing the remediation plan. Set deadlines for completion. Track the progress of the remediation plan and make adjustments as needed.
The CMMC Assessment Process: What to Expect and How to Prepare
Navigating the CMMC Assessment: A Step-by-Step Guide
CMMC Level 1 (Self-Assessment):
-
Preparation: Ensure you’ve implemented the 17 basic safeguarding requirements from FAR clause 52.204-21. Gather documentation to support your implementation.
-
Self-Assessment: Conduct a self-assessment against the Level 1 requirements. Document your findings.
-
SPRS Submission: Enter your assessment results into the Supplier Performance Risk System (SPRS). This step is a requirement for demonstrating Level 1 compliance.
-
Ongoing Maintenance: Conduct annual self-assessments and update your SPRS submission as needed.
CMMC Level 2 (Third-Party Assessment for most contracts):
-
Preparation: Implement the 110 security controls from NIST SP 800-171. Conduct a thorough gap analysis and remediate any identified weaknesses. Gather comprehensive documentation to demonstrate compliance.
-
Selecting a C3PAO: Choose a Certified Third-Party Assessment Organization (C3PAO) from the CMMC-AB marketplace. Ensure the C3PAO is accredited and experienced.
-
Scoping the Assessment: Work with the C3PAO to define the scope of the assessment, including the systems, data, and personnel involved. Establish a timeline and assessment plan.
-
Assessment implementation: The C3PAO will conduct the assessment, which may include document reviews, system scans, interviews, and physical security inspections. The C3PAO will gather evidence to verify compliance.
-
Reporting and Remediation: The C3PAO will provide a report of their findings, including any identified deficiencies. Address any identified deficiencies and provide evidence of remediation.
-
Certification: If all requirements are met the C3PAO will submit the results and provide a certificate. Annual affirmation is also required.
-
Ongoing Monitoring: Maintain your safety controls and undergo reassessments every three years.
CMMC Level 3 (Government Assessment):
-
Preparation: implementation of CMMC Level 2 compliance. Implement the additional security requirements from NIST SP 800-172. Prepare for a government-led assessment.
-
Scheduling the Assessment: The Defense Contract Management Agency’s Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) will schedule the assessment. This is typically coordinated through your Department of Defense (DoD) contracting activity.
-
Assessment implementation: DIBCAC assessors will conduct the assessment, which may include document reviews, system scans, interviews, and physical security inspections. The assessors will verify compliance with the applicable NIST SP 800-172 controls.
-
Reporting and Remediation: DIBCAC will provide a report of their findings, including any identified deficiencies. Address any identified deficiencies and provide evidence of remediation.
-
Certification: If all requirements are met DIBCAC will certify the organization. Annual affirmation is also required.
-
Ongoing Monitoring: Maintain your safety controls and undergo reassessments every three years.
Certified Third-Party Assessor Organizations (C3PAOs) play a vital role in the CMMC ecosystem
C3PAOs are authorized to perform independent assessments of organizations seeking CMMC Level 2 certification. This involves evaluating whether a company’s cybersecurity practices align with the NIST SP 800-171 requirements. They offer unbiased assessments, ensuring that Department of Defense (DoD) contractors meet the necessary security standards. This third-party validation adds credibility to the certification process. After completing an assessment, C3PAOs submit their findings to the CMMC Accreditation Body (Cyber-AB). These results are crucial for determining whether an organization receives CMMC certification. C3PAOs must adhere to strict ethical and professional standards, ensuring the integrity of the assessment process. They undergo rigorous vetting by the Cyber-AB.
Preparing for a CMMC Assessment
1. Establish a Dedicated Team:
Assemble a team with representatives from IT, security, legal, and applicable business units. Assign clear roles and responsibilities. Ensure the team understands the CMMC requirements.
2. Conduct a Thorough Gap Analysis:
Use NIST SP 800-171 or 800-172 as your baseline. Identify and document all gaps between your current security posture and the required CMMC level. Develop a remediation plan with timelines and assigned responsibilities.
3. Focus on Documentation:
Create or update all required safety policies. Ensure they are comprehensive, accurate, and reflect actual practices. Maintain detailed system configurations, network diagrams, and data flow diagrams. Document hardware and software inventories, including patch levels and security settings. Develop and document an incident response plan. Maintain records of past safety incidents and responses. Document user access controls, including user accounts, permissions, and access logs. Maintain records of user training and safety requiring activities. Document all changes to systems and configurations. Maintain records of security assessments and vulnerability scans. Keep accurate records of all security awareness and training programs. Track employee participation and completion.
4. Evidence Collection:
Capture screenshots of system configurations and safety settings. You will need to maintain detailed system logs and audit trails. Collect evidence of policy implementation, for example, meeting minutes, training records, and system logs. Maintain reports of vulnerability scans and penetration tests. You will need to document remediation efforts and results. Take photos or videos of physical safety measures, for example, access controls and surveillance systems. You will also need to maintain visitor logs. Prepare employees for potential interviews by the assessor. You will need to ensure they understand their roles and responsibilities in maintaining security. Practice answering potential questions with employees is a good way to prepare.
5. Organize and Centralize Documentation:
Use a secure and organized document management system. Ensure all documentation is easily accessible to the assessment team. Create an index or table of contents to facilitate navigation.
6. Conduct Internal Audits:
Perform internal audits to verify the effectiveness of your controls. Identify and address any remaining gaps or weaknesses. Use internal audit findings to improve your documentation and evidence collection.
7. Engage with a C3PAO (If applicable):
If pursuing Level 2, establish early communication with your chosen C3PAO. Seek their guidance on required documentation and assessment. Have a pre-assessment meeting if possible.
8. Maintain Continuous Monitoring:
Implement continuous monitoring of your security controls. Regularly review and update your documentation. Stay informed about changes to CMMC requirements.
Documenting Your Compliance Efforts: Maintaining Ongoing Security
Maintaining CMMC Compliance: Documentation and Continuous Improvement
1. Demonstrating Compliance:
Comprehensive documentation provides a clear audit trail, demonstrating that your organization has implemented and maintained the required security controls. This is essential during CMMC assessments and other audits. Documentation serves as concrete evidence that your policies are not just words on paper, but are actively enforced.
2. Facilitating Effective Safety Operations:
Well-maintained documentation ensures consistency and standardization in security requirements across the organization. This reduces the risk of errors and omissions. Documentation facilitates knowledge transfer between employees, especially during on boarding or when personnel changes occur. Detailed documentation of systems, configurations, and incident response procedures is crucial for effective incident response. It allows you to quickly identify and address safety incidents. Documentation of system configurations allows for better control of changes to those configurations.
3. Reducing Risk and Liability:
Documentation of risk assessments and mitigation strategies demonstrates that your organization is proactively managing cybersecurity risks. In the event of a breach, thorough documentation can help demonstrate that your organization took reasonable steps to protect sensitive information, potentially mitigating legal liability.
4. Streamlining Assessments and Audits:
Well-organized documentation streamlines the assessment and audit process, and saving time. Accurate and up-to-date documentation reduces the risk of errors and discrepancies during assessments.
5. Continuous Improvement:
Regularly reviewing documentation can help identify weaknesses in your practices and subjects for improvement. Documentation allows you to track your progress in implementing and maintaining controls.
-
Key Documentation Areas:
-
Policies
-
System Configurations
-
Network Diagrams
-
Incident Response Plans
-
Access Control Records
-
Vulnerability Scan Reports
-
Training Records
-
Risk Assessments
-
Data Flow Diagrams
-
Organizations must continually monitor and update security controls
1. Evolving Threat Landscape:
Cyber threats are constantly evolving, with new vulnerabilities and attack vectors being determined daily. Continuous monitoring allows organizations to detect and respond to these emerging threats in a timely manner. Proactive monitoring and improvement are essential for staying ahead of sophisticated adversaries.
2. Maintaining CMMC Compliance:
CMMC compliance is not a one-time event. It requires continuous monitoring and improvement to maintain certification. Continuous monitoring demonstrates your organization’s commitment to cybersecurity and due diligence in protecting sensitive information. CMMC requirements may evolve over time, and continuous monitoring allows you to adapt to these changes.
3. Detecting and Responding to Safety Incidents:
Continuous monitoring enables the early detection of incidents, minimizing the potential damage. Real-time monitoring allows for rapid response to incidents, reducing downtime and data loss. Monitoring data provides valuable insights for incident analysis and post-incident review.
4. Improving Security Posture:
Continuous monitoring helps identify weaknesses in your controls and areas for improvement. Monitoring data provides metrics to measure the effectiveness of your controls. Continuous monitoring enables data-driven decisions for improving your posture.
5. Ensuring Business Continuity:
Continuous monitoring helps minimize disruptions caused by safety incidents, ensuring business continuity. It helps protect critical assets and data, ensuring the continued operation of your business. Robust security controls and continuous monitoring build customer trust and confidence.
Maintaining CMMC certification
1. Continuous Monitoring and Improvement:
Utilize SIEM systems, vulnerability scanners, and intrusion detection/prevention systems to continuously monitor your security requirements. Keep all policies and system documentation current. Document any changes to your controls or systems. Perform internal audits to assess the effectiveness of your controls. Identify and address any gaps or weaknesses. Keep up to date of emerging cyber threats and vulnerabilities. Update your controls and incident response plans accordingly. Maintain a rigorous patch management process to ensure that systems and applications are up-to-date.
2. Preparing for Reassessments:
Familiarize yourself with the latest CMMC requirements and assessment actions. Pay attention to any changes or updates. Perform a thorough gap analysis to identify any areas where your security posture may have weakened. Address any identified gaps promptly. Compile all necessary documentation and evidence to demonstrate compliance. Ensure that your documentation is organized and easily accessible. Establish early communication with your C3PAO to discuss the reassessment process. Seek their guidance on any questions or concerns. Ensure that all employees are up-to-date on security requirements. Verify that your backups are working, and that you have a recovery plan in place.
3. Maintaining Certification:
Ensure that all employees consistently adhere to your security requirements. Continuously monitor and maintain your security requirements. Develop and maintain an incident response plan. Practice incident response procedures through regular drills. Keep documentation updated as changes occur. Monitor the CMMC-AB website and other applicable sources for updates and changes to the CMMC program. Remember that in level 2 and 3, that annual affirmation is required. Keep accurate records of all activities, including incident reports, vulnerability scans, and training records. By following these steps, you can ensure that you are well-prepared for reassessments and maintain your CMMC certification.
Resources and Support: Navigating Your CMMC Journey
Here are the links to official CMMC resources:
-
Office of the Under Secretary of Defense for Acquisition & Sustainment (OUSD A&S) CMMC Website (DoD Official Website):
-
This is the primary source for official CMMC information from the DoD:
-
-
CMMC Accreditation Body (Cyber-AB):
-
The Cyber-AB is the independent accreditation body responsible for implementing and managing the CMMC program:
-
-
National Archives and Records Administration (NARA) CUI Registry:
-
This is the official location for the CUI registry, and is vital for understanding CUI.
-
These resources will provide you with the most accurate and up-to-date information regarding CMMC.
Don’t Wait, Secure Your Future: Take Action on CMMC Compliance Today!
Here’s what you need to do NOW:
Navigating the complexities of CMMC compliance can be daunting, but you don’t have to face it alone. FirstCall offers a unique advantage: we’re a CMMC compliant MSP currently pursuing C3PAO accreditation. This means we understand the requirements intimately, from both the provider and auditor perspectives.
We’ve walked the path you’re about to embark on, and we’re equipped to guide you every step of the way. Don’t risk costly delays or non-compliance. Contact FirstCall today, and let us leverage our firsthand experience and in-depth expertise to streamline your CMMC journey, ensuring your organization achieves and maintains the necessary security posture.





